Best SaaS Security Practices for 2025
SaaS applications offer rapid deployment and scalability, but this convenience comes with a significant security challenge. As you add more services, it becomes increasingly difficult to track sensitive data, manage user access, and mitigate potential threats.
The stakes are high. Following a series of major data breaches, a staggering 93% of security specialists have increased their SaaS security budgets, signaling a major shift in priorities.
The 'set it and forget it' approach is no longer viable. Security must be an integrated, managed process at every level of the system.
The Evolving Landscape of SaaS Security
SaaS security is undergoing a tectonic shift, driven by several powerful trends that expand the modern attack surface:
- AI-Powered Attacks: Cybercriminals now use AI not just for password cracking but also for automatically harvesting credentials from misconfigured public repositories and cloud resources, paving the way for mass data theft.
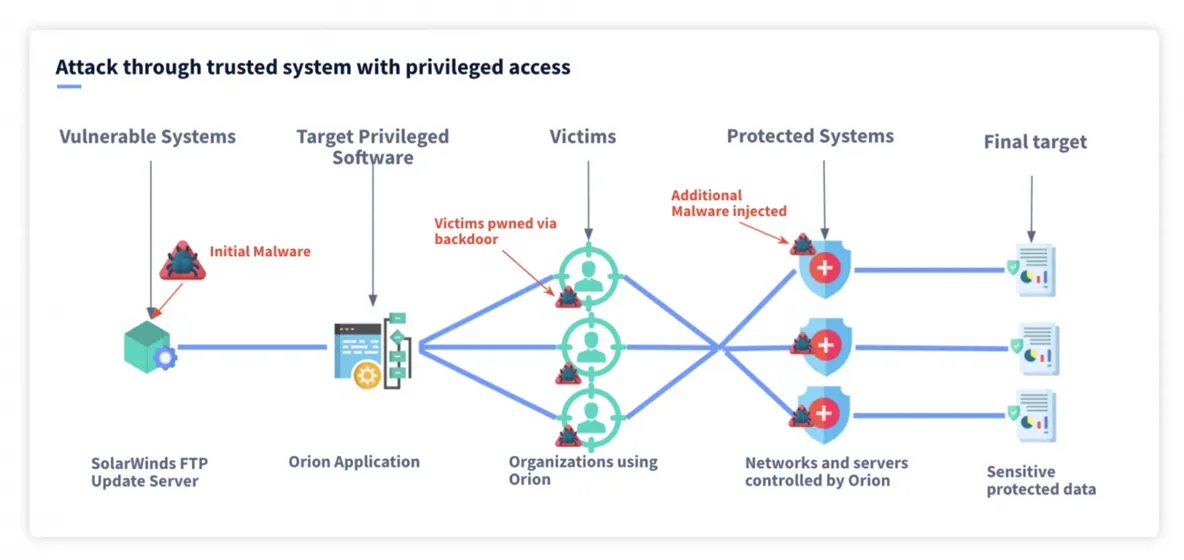
- Supply Chain Vulnerabilities: Software supply chain attacks increasingly target SaaS ecosystems. A single compromised API, plugin, or open-source library can poison the entire dependency chain, leading to a massive breach.
- Complex Architectures: Modern infrastructures built on microservices, serverless functions, and multi-cloud environments create an exponentially larger and more complex attack surface to defend.
Why Invest in a Proactive Security Strategy?
AI-powered attacks, weak integration points, and complex architectures form an interconnected web of threats that demand immediate attention. A well-designed SaaS security strategy offers tangible benefits:
- Data Protection: Encryption, strict access policies, and continuous monitoring are essential for protecting critical data—including customer information, IP, and financial records—and ensuring business continuity.
- Early Threat Detection: Centralized logging, continuous monitoring, and well-defined incident response plans enable teams to detect, contain, and mitigate threats before significant damage occurs.
- Secure Integrations: Architect your API, plugin, and third-party service connections so that a compromise in one component doesn't cascade and bring down the entire ecosystem.
- Compliance and Risk Management: With tightening regulations worldwide, proactive security measures simplify adherence to standards like SOC 2, HIPAA, and GDPR, helping manage legal and financial risks.
Top SaaS Security Practices for 2025
Shift Left with DevSecOps
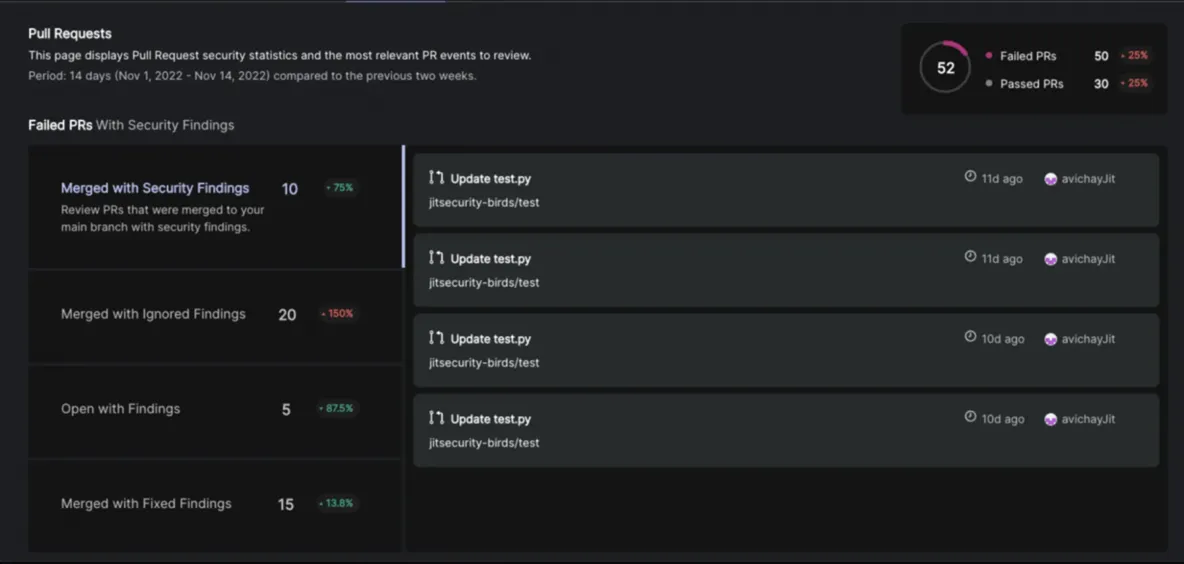
When teams deploy code daily, security threats are inevitable without automated checks. Integrating Static (SAST) and Dynamic (DAST) Application Security Testing tools into the CI/CD pipeline provides developers with immediate feedback. This allows vulnerabilities and insecure dependencies to be identified and resolved during the coding phase, not after deployment.
Implement Threat Modeling
During the design phase, creating models of potential threats helps visualize how data flows through the system. This practice uncovers vulnerabilities early when fixes are cheaper and easier to implement. Ask key questions like:
- Where is sensitive data transferred?
- Who has access to it?
- What external systems does the application interact with?
Advance Your Identity & Access Management (IAM)
Static access models are dangerous. Adhering to the principle of least privilege is crucial. Implement a centralized IAM solution with mandatory multi-factor authentication (MFA) and granular access policies. Enhance security further with dynamic authorization, which can verify a user's geolocation, device health, or even the time of day before granting access.
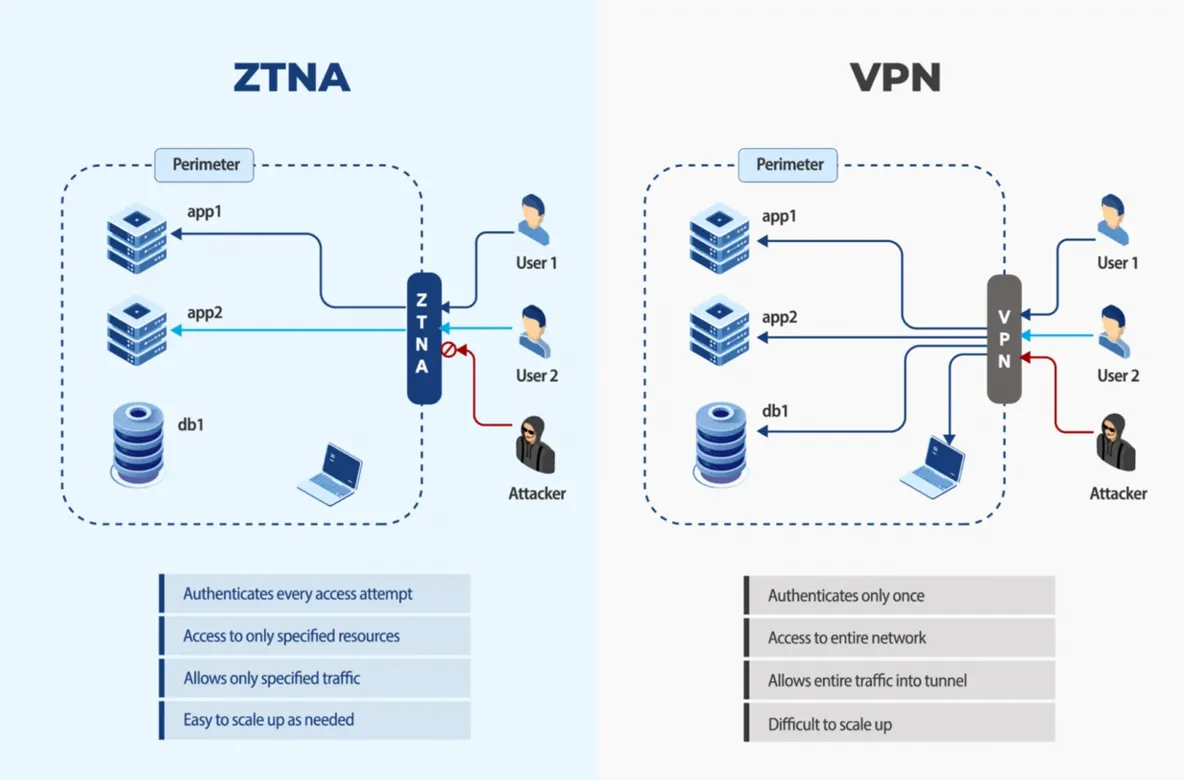
Adopt a Zero Trust Architecture (ZTA)
The concept of a trusted "internal" network is obsolete. Zero Trust Network Access (ZTNA) verifies identity and context for every access request, granting access only to specific applications rather than the entire network. To bolster this approach, use micro-segmentation to divide your infrastructure into small, isolated segments, which drastically reduces an attacker's ability to move laterally if they breach the perimeter.
Automate Cloud Configuration Monitoring
Misconfigurations are a leading cause of data breaches. With rapid deployment cycles, manual audits can't keep up. Use tools like KICS, CloudSploit, or native services such as AWS Config to automatically and continuously scan your cloud environment for vulnerabilities and policy deviations.
Secure APIs with OAuth 2.0 and OIDC
Public APIs are prime targets for token theft and replay attacks. The best practice is to combine OAuth 2.0 for delegated authorization with OpenID Connect (OIDC) for authentication. This is achieved by using an Identity Provider (IdP) like Auth0 or Okta.
- Use short-lived access tokens with strictly configured scopes (e.g.,
read:tenantto allow reading data but not modifying it). - For sensitive resources, use token introspection endpoints so the server can verify a token is active before granting access.
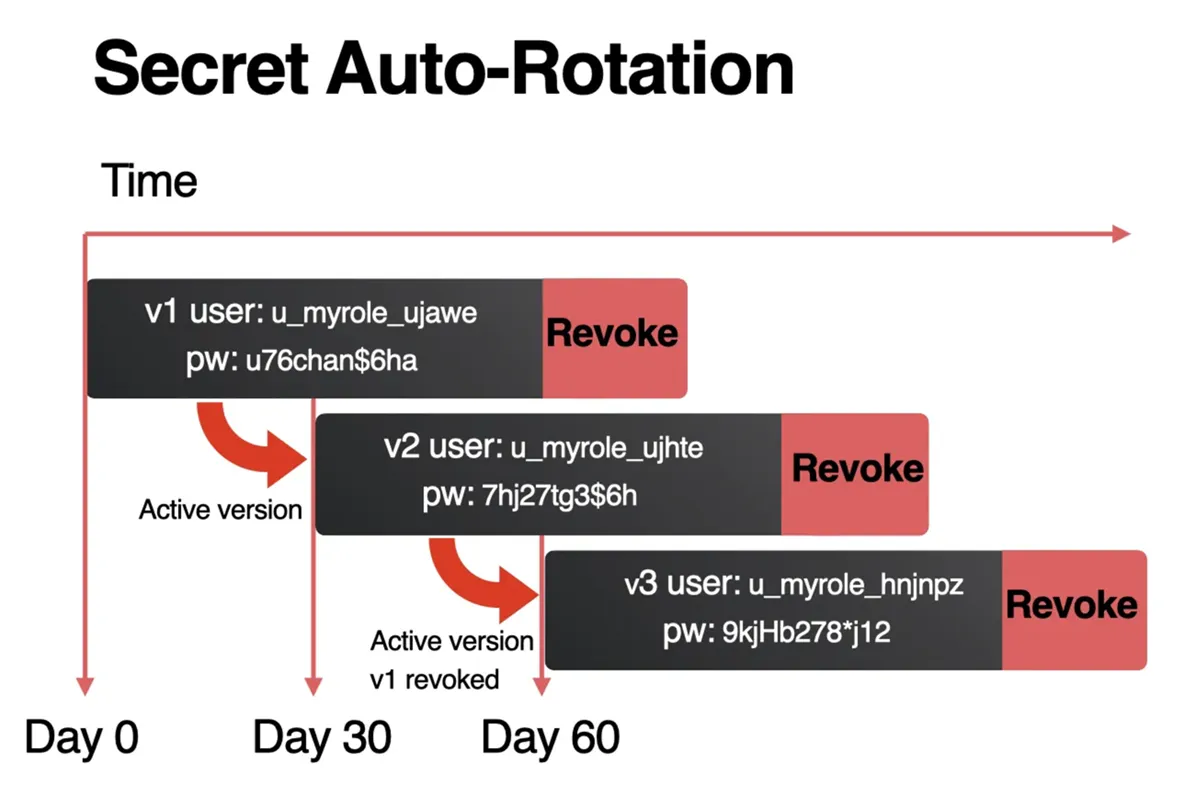
Automate Secrets Management
Manually managing secrets like API keys and database credentials is impractical at scale. Use a specialized tool like Azure Key Vault or AWS Secrets Manager to automate secret rotation. Crucially, set rotation policies at the individual secret level, not globally. High-priority secrets, for example, might require rotation every 24 hours.
Secure Your Container Architecture
Container security starts at the build stage. Use minimal base images, employ multi-stage builds to remove unnecessary libraries, and integrate automated vulnerability scanners like Trivy. In production, avoid running containers as root, strip unnecessary process capabilities, and restrict system calls using seccomp profiles to significantly reduce the attack surface.
Effective SaaS security is not an afterthought; it must be woven into your daily workflows. This means integrating security into DevOps, diligently managing access, continuously monitoring cloud environments, and automating secrets management.
The sooner these practices become standard procedure for your team, the lower the risk that a new vulnerability or accidental leak will turn into a major business disruption.