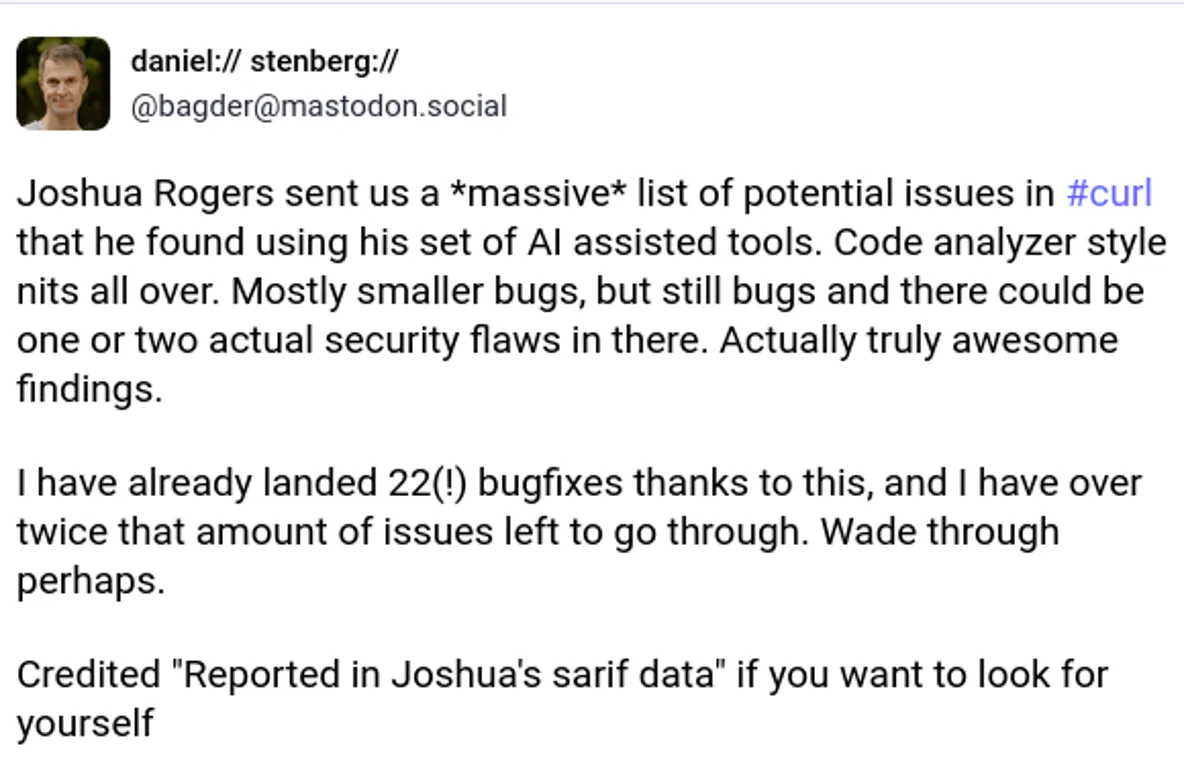
Daniel Stenberg, the author of curl, reported that AI code verification tools helped discover 50 errors in the utility
AI Tools Uncover 50 Bugs in Curl, Changing Creator's Stance
Daniel Stenberg, the creator of the widely-used open-source utility curl, recently announced a significant shift in his perspective on AI-driven code analysis. This change came after security researcher Joshua Rogers used a suite of AI tools to successfully identify and report approximately 50 bugs in the project.
From AI Skepticism to Appreciation
This development is particularly noteworthy because Stenberg had previously declared that the curl project would no longer review AI-generated vulnerability reports submitted through platforms like HackerOne. He cited the overwhelming volume of low-quality submissions, which drained the team's resources as they spent far more time verifying the reports than the AI took to generate them.
However, the reports from Rogers demonstrated that the issue wasn't the technology itself, but how it was applied. His submissions were not only credible but highly valued by the curl team.
Most of them were minor bugs and nits in the style of a regular static code analyzer, but they were still bugs that we are better off fixing. Some of the discovered issues were quite impressive finds.
The Right Tools in the Right Hands
Stenberg confirmed to The Register that he had already accepted around 50 fixes based on Rogers' findings. The researcher used a variety of AI-powered scanning tools to achieve these results:
- Almanax
- Corgea
- ZeroPath
- Gecko
- Amplify
Powerful tools in the hands of a smart person is a good combination, for sure. It has always been.
The discovered issues ranged from minor code style infractions to potentially serious security vulnerabilities, proving that AI can be a powerful ally in maintaining code quality and security when wielded by a knowledgeable expert.
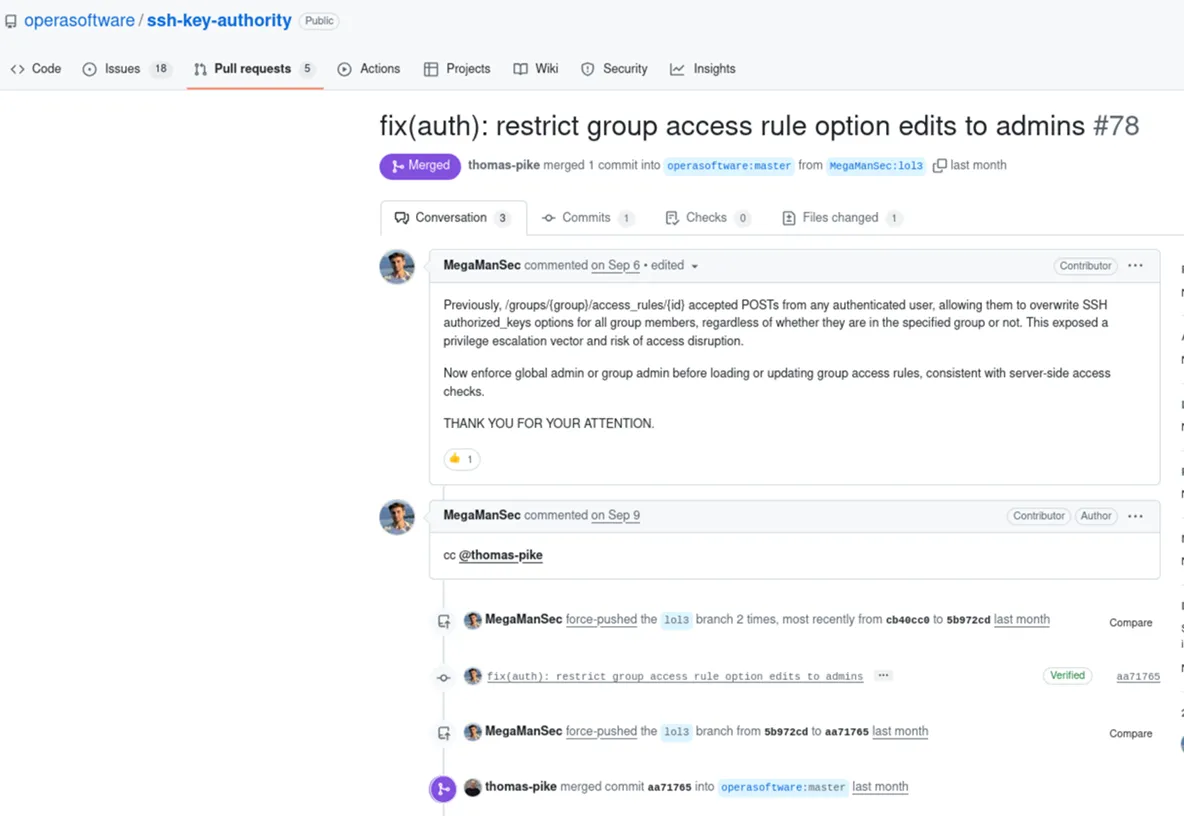
Rogers' efforts have also uncovered critical vulnerabilities in other projects, including the source code of his former employer, Opera Software, where a bug was patched in early September 2025.